A faux Aadhaar offered at a lodge and a SIM card procured with that ID performed an important half in cracking the March 1 Bengaluru cafe blast case, stated sources.
This SIM card, stated a supply, was used within the cellphone of one of many individuals who offered logistics assist for the blast.
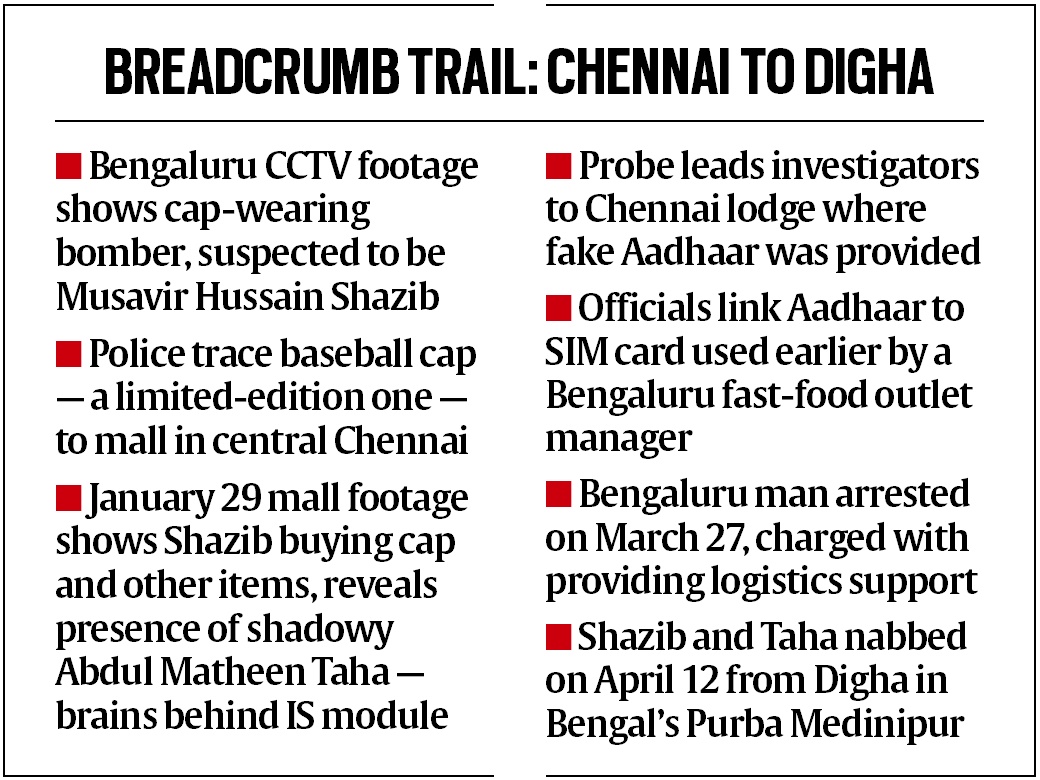
Investigators got here throughout this key lead in mid-March because the path of a baseball cap abandoned by the Rameshwaram Cafe IED bomber led them to one of many lodges in Chennai the place he and another suspect had stayed .
On March 27, based mostly on the findings from searches at Chennai and a number of locations in Karnataka, the NIA arrested the logistics support provider — a 30-year-old supervisor of a Bengaluru quick meals outlet named Muzammil Shareef.
The identical day, the Nationwide Investigation Company (NIA) additionally introduced for the primary time that the perpetrators of the blast, which left 9 individuals injured, had been recognized from earlier investigations in Chennai and Bengaluru as Musavir Hussain Shazib, 30, and Abdul Matheen Taha, 30, two terror suspects from Karnataka who had been lacking since 2020 after being linked to an IS recruitment plot.

 The Rameshwaram cafe in Bengaluru’s Whitefield space reopened every week after the blast. (Specific Picture)
The Rameshwaram cafe in Bengaluru’s Whitefield space reopened every week after the blast. (Specific Picture)
Whereas the arrested individuals used elaborate strategies to cowl their tracks — a number of SIM playing cards obtained with faux identities, second- and third-hand cellular handsets, faux ID playing cards, encrypted chats for communication — they left clues in Chennai.
“A cellphone quantity linked to Shareef was discovered from paperwork offered at a lodge the place the accused stayed in Chennai. This offered a breakthrough,” a police supply stated. Sources stated the SIM card had been utilized in a cellphone that was with Shareef 4 or 5 months in the past, sources stated
Sources stated Shareef is suspected to have helped the principle suspects extensively by offering them SIM playing cards and faux IDs throughout a number of conferences.
 Breadcrumb path: Chennai to Digha
Breadcrumb path: Chennai to Digha
The NIA indicated on March 29 that Taha stayed at lodging amenities in Chennai in February, forward of the bombing, utilizing the identities of Vignesh B D and Sumit. The NIA has indicated that Shazib was utilizing a faux ID of Mohammed Juned Sayed in Chennai.
In line with sources the group by no means bought a brand new SIM card or cellphone however solely dealt with those who had modified a number of fingers. In a single occasion, as many as 150 SIMs had been discovered to have been used with a cellphone linked to a suspect.
Following the arrest of Shazib and Taha in West Bengal’s Purba Medinipur district on April 12, businesses have reported discovering as many as 35 SIM playing cards other than faux ID credentials like Aadhaar playing cards and driving licences.
Supply of funds
One of many key angles the NIA is investigating relating to the actions of Taha and Shazib since they disappeared from the safety radar in January 2020 when businesses in Karnataka, Tamil Nadu and the NIA started in search of them in an inter-state IS recruitment and radicalization case is the supply of the funding of the duo.
Taha is alleged to have been receiving funds by means of an unknown cryptocurrency route the place he would switch crypto foreign money to the crypto accounts of associates, acquaintances and accomplices for conversion to Indian rupees for functions like funding a plot and funding their day by day residing and way of life.
Taha and Shazib dealt solely in money on the lodges they stayed at, stated sources conversant in investigations.
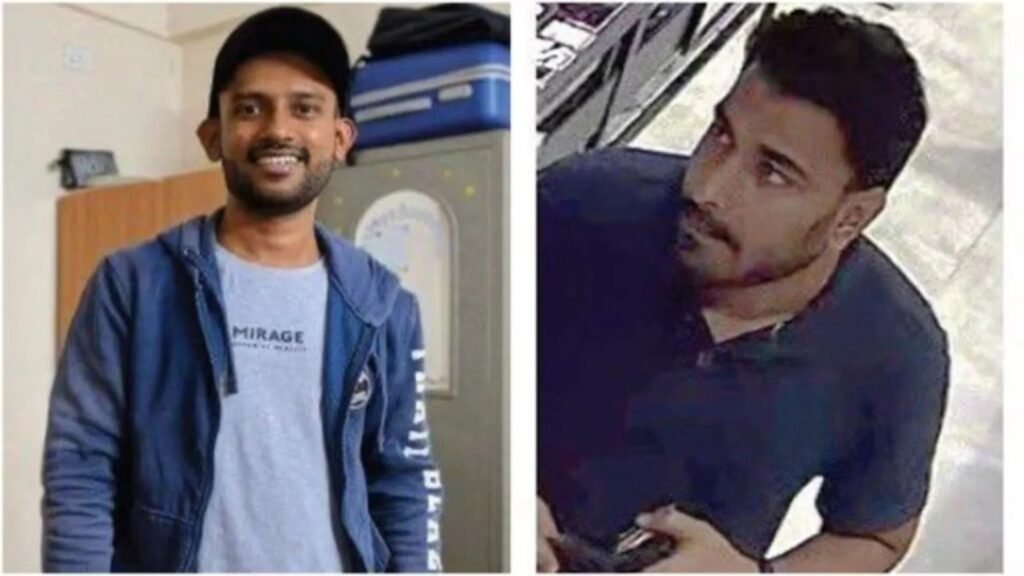
 Adbul Matheen Taha (left) and Mussavir Hussain Shazib had been traced out to their hideout close to Kolkata. (File Photographs: X/@NIA_India)
Adbul Matheen Taha (left) and Mussavir Hussain Shazib had been traced out to their hideout close to Kolkata. (File Photographs: X/@NIA_India)
The probe has discovered that Taha used varied conduits – together with stolen identities and the IDs of individuals recruited for the IS trigger in several elements of India – to switch crypto foreign money to Muzammil Shareef to rearrange logistics for the March 1 cafe blast operation.
Sources stated a small amount of cash (valued at lower than Rs one lakh) was obtained by Shareef by means of the crypto foreign money path to finance the cafe blast preparations and execution. Shareef is alleged to have organised supplies for the execution of the blast together with SIM playing cards and telephones below faux identities.
The NIA has questioned a childhood buddy of Taha, from Shivamogga, over cryptocurrency transactions carried out by Taha through the use of the username of the childhood buddy Sai Prasad who’s a small-time BJP employee.
The place had been the lacking suspects within the final 4 years?
In line with police sources, Taha and Shazib who could have travelled overseas previous to 2020 after being impressed by the Islamic State, had been residing in India over the past 4 years ceaselessly altering their areas.
They’re alleged to have moved between West Bengal, Maharashtra, Karnataka, Tamil Nadu, Kerala and Andhra Pradesh within the final 4 years for brief stays starting from just a few days to 6 months.
“They stayed in low cost lodging amenities and appeared to have travelled by street or rail however they wore costly garments and ceaselessly moved areas. They’re each unemployed and the supply of funds that enabled their way of life is a key a part of investigations,” sources stated.
Jail leg of investigation
Within the early a part of the probe of the cafe blast (which was taken up by the NIA on March 3) businesses investigated a key member of the Shivamogga IS module – Maaz Muneer Ahmed, 26, who has been lodged in jail since September 2022 following his arrest in a trial IED blast case close to the module’s hometown of Thirthahalli within the Shivamogga area.
Searches had been carried out within the jail on March 14 by the NIA and a reminiscence card was discovered. On the identical day Maaz Muneer was taken into custody by the NIA for seven days. He was later named as certainly one of 4 accused within the March 1 blast case together with Shareef, Taha and Shazib.
Sources stated that Maaz Muneer was speaking with the 2 lacking suspects and was conscious of the cafe bombing plot regardless of being in jail.
The IED used for the cafe blast was equivalent by way of its building and supplies used as an IED that unintentionally exploded in an autorickshaw within the Mangaluru area of coastal Karnataka on November 19, 2022 when the IED was being carried by Mohammed Shariq, 24, a member of the Shivamogga module who was arrested after the unintentional blast.
The IEDs constructed utilizing simply obtainable supplies – like gunpowder and sulphur as explosives -are reported to have been constructed by Shariq (within the Mangaluru case) and Taha/Shazib (within the Rameshwaram Cafe blast case) through the use of do-it-yourself strategies propagated by the Islamic State linked actors on on-line boards for practically a decade.
The NIA is but to establish the id of an individual going by the identify of “Colonel” who interacted with among the younger, radicalised recruits within the Shivamogga IS module.
As many as 10 members of the module aged between 22 to 26 are in jail at current and the arrest of Taha, Shazib and Shareef takes the overall variety of arrested individuals from the module to 13.